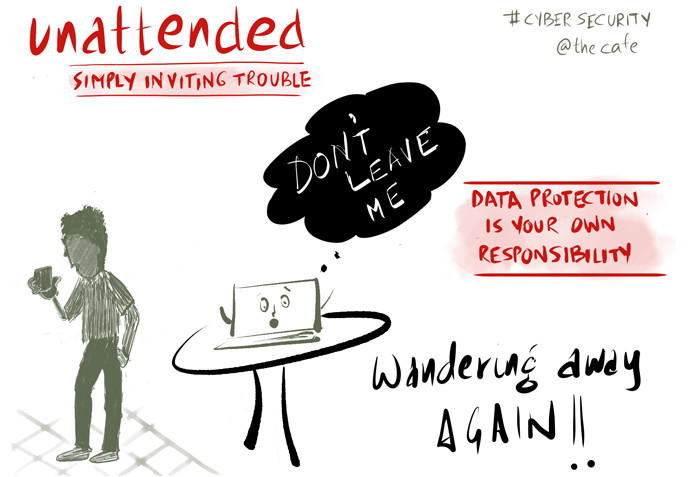
It was a sunny cold winter afternoon… and in a span of a few hours, at the café, I saw unattended laptops (not once or twice but six times, and left by as many people), just waiting to be picked up… When was the last time you strolled away to buy a coffee or turned your back to talk to someone? A security breach waiting to happen.
A false sense of security blinds many startups. You may think that you are too small to matter to cybercriminals, but trends show a relatively sharp increase in hackers targeting smaller (typically more vulnerable) businesses – often with catastrophic results.
Security risks are no longer just about stolen passwords, accidental virus attacks or physical thefts but often cause API disruption, IP theft and Personal Data Breach – all of which can be devastating, particularly for startups. Many startups have fallen victim to extortion, lost credibility with clients, faced market delays and in some instances even been forced to shutdown.
vyn recognised that early, invested from day one and designed a simple approach built on incremental improvements… every single effort, every day makes our product secure, our systems resilient and our processes innovative (not just optimal).
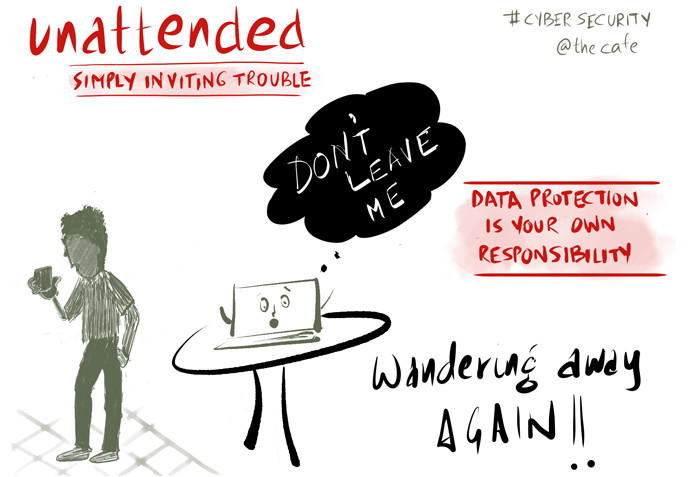
We have once again been certified by IASME to Cyber Essentials and IASME Governance Standard in January 2020 (https://iasme.co.uk/certified-organisations) – a testimony to the integrated effort of our team that has worked so hard to make security not just a foundation for our business, but a differentiator.

Yes, security can be turned from a dull-routine-forced-mandate to an advantage. And while security infrastructure and systems are often overlooked in the early stages of a startup, I would strongly advocate that you start at the very beginning. Adopting strong security practices is much easier when the company is young. And the excuse of limited resources or development constraints is just that – an excuse.
A simple 9-point framework that has worked for us:
- Use the constraint of limited resources and development bandwidth to your advantage – leverage the power of distributed ownership. We believe that Security does not necessarily require an IT department, but depends on team effort – and it is the ownership of each and every employee in the company that builds the security culture, that gets manifested in every intent, every action.
- Imbibe security into the culture. Start by showing that security is important through communication and example. Include it in your new employee induction, but also provide periodic refresher training and spot audits. Be cognizant of the effort needed to sustain it as you move from the startup to a scale-up. Reinforce the value and the differentiators – and stay on the lookout for best practices to adopt or drive.
- Design for continuous improvement. Start small. Do not wait for the perfect process and evolve incrementally.
- Use only secure platforms – partner with vendors who share strong security practices, such as Amazon AWS, Google Apps, Apple MacOS & iOS, Linux and other open source systems.
- Integrate security into all your coding and DevOps. Adding it later will cost you more as you migrate to new infrastructure, change software and tools, or change architectures and rewrite code.
- Enforce simple best practices for core systems – multi-factor authentication, secure communication, data encryption at rest, role-based access control and lock down of all admin accounts.
- Prioritise high-risk areas and focus first on mobile worker security processes. Remote access is the norm today and you cannot control home networks or public networks. Secure your access devices (laptops, mobile phones) and enable advanced security controls on all cloud-based applications. Secure all communication via encryption.
- Plan for faults and breaches. Be prepared – assume that systems and processes can fail. Define and test your processes to handle data breaches, restore backups or any other business-impacting event.
- Perform periodic risk assessment. Identify gaps and fix.
It may seem like a lot of work – but it’s not, if you make it a way of life and let your decisions be driven and tested against these guidelines. You just need to know what to focus on. When you look for a new tool or a platform, select only those that are compliant to the required security standards; when you write a new API use code analysis tools and run vulnerability or penetration tests. When you buy a new device, spend a few hours configuring it for firewalls, antivirus and encryption. When you dispose of an old device, purge the data first.
If everyone takes ownership, it can be done. I can say it from our own experience.
Arti is the co-founder of humanLearning – a fast growing UK-based technology startup that is disrupting business workflows through vyn. vyn combines short structured and searchable videos, dynamic storyboards and event-driven SaaS with machine learning algorithms to make workflows more dynamic and deliver faster business outcomes. Arti can be reached at [email protected].
—
Thank you for reading!
If you would like to know more about vyn, please get in touch with us at [email protected]
Follow vyn on LinkedIn or Twitter to get more insights like this, or sign up to our newsletter.



Leave a reply